BIMI – Brand Indicators of Message Identification
With email impersonation, phishing and spoofing attacks on the rise, email recipients are increasingly suspicious of messages in their inboxes. They have good reason to be. 60% of North Americans say that they or a family member were victims of fraud.
To add another layer of email protection (and create brand visibility), companies can adopt a new standard known as BIMI that is still in its early stages of adoption but promises to take consumer confidence to the next level.
What is BIMI protocol?
BIMI is a proposed standard that allows you to display your company logo in your authenticated email messages when your domain has a DMARC policy in quarantine or rejection mode.
Similar to other protocols, BIMI is a txt record created in the DNS zone. The record points to a URL where your logo is hosted in .svg format, adding it to authenticated emails sent.
How it works?
To implement BIMI, you must first ensure that your domain has the DMARC protocol in quarantine or rejection mode. Then you have to be evaluated and certified by a BIMI certification provider
Then you can apply the following txt record to your DNS
Name: default._bimi.seudominio Type: TXT Value: v=BIMI1; l=https://urllocalhospedado.svg
BIMI supports several logos per domain using what is called selectors. As you can see above, default are the default selectors used in this case. If you want to have different logos for different e-mail sending services you can make use of different selectors.
Why adopt BIMI?
With this simple visual check, recipients can recognize and trust incoming messages.
But if you already have SPF, DMARC and DKIM, why do you need BIMI? Good question. Let’s take a high-level look at each one to identify the main features:
- BIMI: add your logo to your inbox emails so that subscribers can quickly identify your messages and trust that they are yours.
- SPF: authenticates your email to identify email servers that are allowed to send email from a specific domain.
- DKIM: adds a digital signature to emails so that destination email servers know that your domain has sent the message and you are responsible for the content of the message.
- DMARC: specifies destination email servers how to handle emails that are not authenticated using SPF or DKIM (accepting, spamming or rejecting).
Looking at this list of verification methods, BIMI is the only visual clue that a typical email user can use to identify the origin and authenticity of a message. It is therefore a visual way to show your recipients that you have adequate DMARC protection and that email is reliable.
BIMI can help recipients recognize and trust your brand in the inbox. This confidence leads to fewer subscription cancellations and spam complaints, which can play an important role in increasing delivery capacity. Your brand becomes more reliable.
In addition, you get another layer of protection against phishers and spoofers who try to impersonate your brand. Without the standard tracking logo, recipients will be wary of messages that claim to be you. And when BIMI becomes more widely adopted, spam and phishing (in general) will become even more obvious, as they will not have certified and recognizable logos.
Finally, BIMI allows you to market your brand easily and automatically. Recipients will connect the return address, subject line and header text to your logo, helping to further strengthen your brand.
BIMI Roadmap
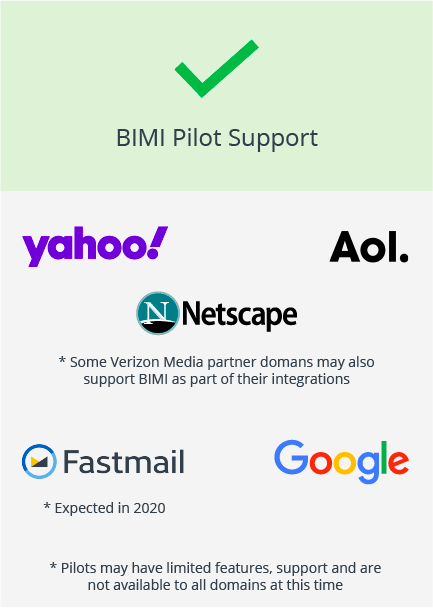
The adoption of BIMI is already significant and the pilot has important players in the market.
So now is a good time to ensure that activities to move the DMARC policy to rejection or quarantine are completed.
Find out how to comply with the DMARC policy at: www.ondmarc.com.br
Request a free trial of your domain now: https://www.managerone.com.br/avaliacao/
Start your project right now!
End-to-end BIMI Certification Project. Contact our team to start your BIMI project. Once the certification is available, companies that already meet the prerequisites can apply for it. At this point, the brand must be analyzed and if necessary adjusted and the DMARC policy correctly configured .;
Setting up the DMARC policy is the most time-consuming step and requires specialized knowledge, so it should be started as soon as possible.

